
WHY
PHANTOM BREACH IS
DIFFERENT.
Phantom Breach is different by design. Most security platforms focus on reactive detection or intrusive control. Phantom Breach is built around continuous visibility, evidence driven intelligence, and intentional response. Our architecture separates observation, intelligence, and action so security teams can understand what is actually happening before deciding how to respond.
By combining high fidelity telemetry, tenant isolated architecture, forensic intelligence, and forward looking cryptographic awareness, Phantom Breach provides clarity in environments where complexity and uncertainty are the norm. This approach enables organizations to validate security posture, reduce blind spots, and adapt as threats evolve without relying on assumptions or opaque automation.
Phantom Breach is designed for organizations that value precision, transparency, and long term resilience over one size fits all security solutions.

OUR PLATFORM
How The Phantom Breach Platform Works
HALOx™ Sensor.
Detect with HALOx™. Learn globally. Act intentionally. HALOx provides high fidelity detection and deep endpoint telemetry, surfacing early indicators of malicious activity without enforcing control or impacting system performance. Observed signals are correlated across the platform to support informed, policy driven response.
Policy Driven Response
Security actions are coordinated externally based on observed telemetry, preserving endpoint integrity while enabling fast and intentional response.
Cloud Intelligence.
Aggregates and correlates telemetry from HALOx™ sensors, continuously learning from global patterns to produce signed, real time intelligence used for detection, prioritization, and policy governed response.
Modular capabilities built on the Phantom Breach Platform. Deploy what you need, scale as you grow.
01
PhantomHQ™
PhantomHQ™ provides a unified view of telemetry, intelligence, and response workflows across isolated tenant environments.
02
GhostTrace™
GhostTrace™ reconstructs activity timelines and adversary behavior using correlated high-fidelity telemetry.
03
BreachWatch™
BreachWatch™ continuously surfaces indicators of elevated risk and potential compromise before incidents escalate.
04
PhantomDefense™
PhantomDefense™ correlates sensor and platform signals to generate prioritization, policy guidance, and response recommendations.
05
PhantomQ™
PhantomQ™ provides visibility into cryptographic posture and post-quantum risk to support long-term resilience planning.
06
Amethyst™
Amethyst™ delivers intent-first network intelligence, reconstructing attack chains and recommending high-confidence disruption points with governed response.
PHANTOM BREACH
PROACTIVE SOLUTIONS
Geographic Endpoint Visibility & Enforcement Context.
Real-time geographic awareness powered by HALOx™ and enforced through PhantomDefense™.

How It Works.
DETECTION →
CONTEXT →
INTELLIGENCE
-
HALOx™ Sensor captures high-fidelity telemetry from endpoints, including network behavior, domain interactions, and contextual location signals.
-
These signals are correlated within the platform to establish geographic and behavioral context for endpoint activity.
-
PhantomDefense™ analyzes this context to generate risk scoring, alert prioritization, and actionable security insights.
The result is a live geographic and behavioral view of endpoint risk, enabling informed security decision-making.

GEOGRAPHIC VIEW
What the Geographic View Shows
The geographic endpoint view enables
teams to:
Phantom Breach provides a real-time
visualization of active endpoints by region
and inferred location. Security teams can
identify anomalous access patterns,
unexpected geographic behavior, and
correlate suspicious domains or network
activity to specific endpoint locations.
Teams can track risk concentration and
behavioral spread across environments,
gaining insight into how threats manifest
geographically.
This view reflects context-rich, correlated
intelligence, not raw telemetry alone.

VPN STATUS
The geographic view also indicates when an endpoint’s observed location reflects VPN usage rather than physical presence. This added context helps security teams accurately interpret location-based activity and avoid false assumptions during investigations. By combining VPN awareness with local enforcement, Phantom Breach enables more precise, location-aware security decisions.

HALOx™ SENSOR TAMPERING
The platform continuously validates sensor health and integrity to ensure endpoint telemetry can be trusted. Real-time tamper detection identifies attempts to disable, manipulate, or evade the HALOx™ sensor, immediately flagging abnormal conditions. This ensures enforcement and intelligence decisions are based on verified, uncompromised endpoint signals.
REAL-TIME VISIBILITY
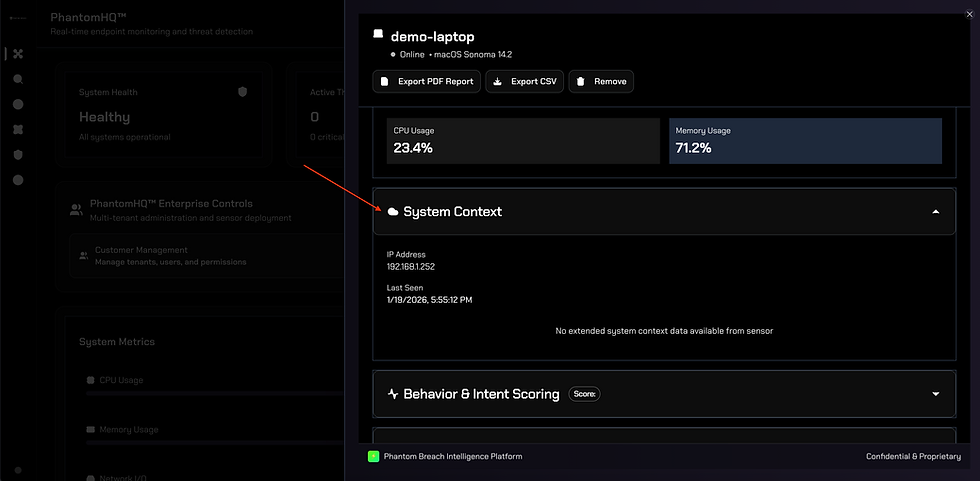
The System Context panel provides real-time visibility into an endpoint’s network and runtime state, including IP address and last-seen activity. This contextual data helps security teams understand how an endpoint is currently connected and whether its behavior aligns with expected usage patterns. When combined with detection and enforcement signals, system context ensures investigations are grounded in current, reliable endpoint reality.
DRILLDOWN PANELS
HALOx Sensor Endpoint Telemetry Panels
HALOx delivers high fidelity endpoint telemetry through unified drilldown panels that provide clarity, context, and trust. The panels present a real time view of endpoint performance, identity, behavior, and security posture without enforcing control on the device.
The platform observes system activity, user context, application behavior, data movement, and operating system signals, then correlates this telemetry to support investigation, validation, and evidence driven security decisions. AI assisted analysis helps prioritize risk and highlight meaningful patterns, while sensor health and integrity indicators ensure the data can be trusted. By correlating signals across endpoints, identities, and networks, Phantom Breach enables teams to understand what is happening and identify anomalous behavior without intrusive endpoint enforcement.
